Getting Started
"AttachéCase4" is a powerful file/folder encryption software that
uses the world's standard encryption algorithm,
while focusing on simplicity and ease of use for daily use.
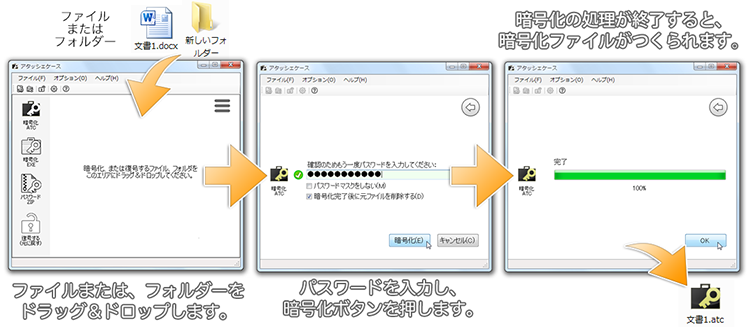
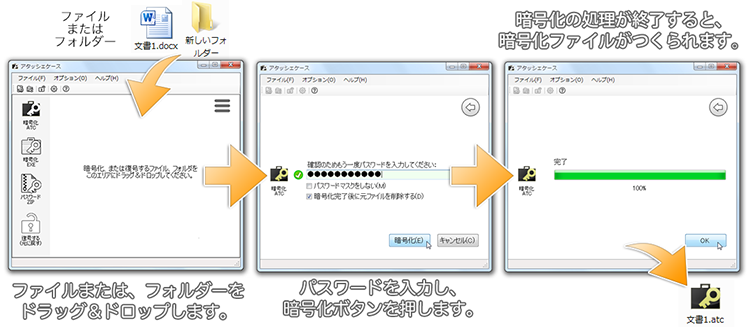
You can easily encrypt a file by simply dragging and dropping it and entering a password,
or if you drag and drop an entire folder,
it will create a single encrypted file (pack the entire folder).
During encryption, the data is compressed, so the size of the file becomes compact.
Decryption can also be done by simply dragging and dropping or
double-clicking and entering the password to restore the original files and folders.
It can also be output as an executable (*.exe) file,
so you can pass the encrypted file to someone who does not have an AttachéCase,
and they can decrypt it.
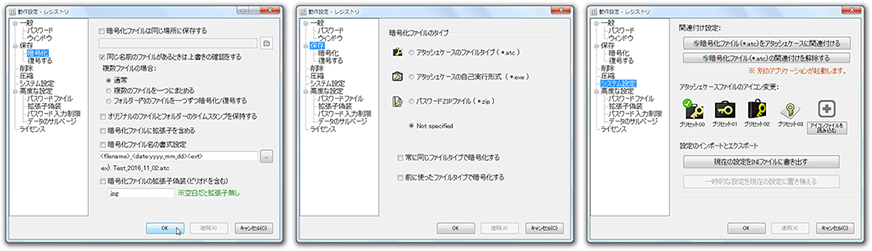
Extensive operation settings
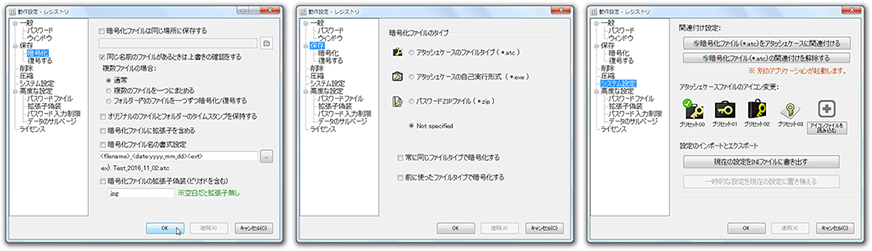
There are options such as specifying the save location,
deleting the file completely after processing,
storing different passwords for each encryption/decryption,
adjusting the compression ratio, limiting the number of password entries,
and destroying data. Command line options are also available.
Adopted the world standard cryptographic algorithm
The encryption algorithm is based on the algorithm selected by
NIST: http://csrc.nist.gov/
in October 2000 as the next-generation encryption standard,
AES (Advanced Encryption Standard).
In adittion, an initialization vector (IV) is generated by
random numbers and then encrypted in CBC mode to prevent analysis by a third party.
(-> For details, please refer to the
"Encryption Algorithms" page.)
The "AttachéCase" has been developed as an open source software,
but since ver.4, it has been available for commercial use only for a fee.
(-> For details, please refer to the
"Commercial Use" page.)
Environment
It can be used in the following environments.
 NET Framework 4.5 later
NET Framework 4.5 later
 macOS 10.14 (macOS Mojave) later
macOS 10.14 (macOS Mojave) later
.NET Framework 4.5
is required to run Windows; nothing needs to be installed for Windows 10
(it is installed by default).
Setup
Install
- When installing from the installer ( atcs4***.exe )
Just double-click the installer ( atcs4***.exe ) and
follow the instructions of the setup wizard to install.
There is almost nothing to be configured by the user.
- When installing from the zip file ( atcs4***.zip )
Please overwrite all files to the previously used folder.
If the folder is changed, the extension association settings, etc. will be invalid.
If you want to change the folder,
follow the instructions in the next section to remove the
old AttachéCase and then reinstall it.
Unistall
- If you installed from the installer ( atcs4***.exe )
Select "AttachéCase" from "Programs and Functions" of "Control Panel"
(Windows XP etc. from "Add / Remove Programs") and delete it. However,
if you want to cancel the association setting with the extension (* .atc),
please refer to the following "How to disassociate" before doing.
- If you installed from the zip file ( atcs4***.zip )
Delete the entire folder containing the AttachéCase.
However, if you want to remove the association setting with the extension (*.atc),
please refer to the following items before doing so.
To remove an association
If you want to cancel the association setting to * .atc file,
launch "AttachéCase", select "Settings" -> "System",
and then push "Disassociate encrypted file(*.atc) with AttachéCase" button.
The association settings are deleted from the system.
For Windows 10, you will be asked for elevating administrators when setting.
If you perform the uninstaller or the above method,
the registry information will be deleted.
If you want manual deletion for some reason, delete the following registry.
HKEY_CURRENT_USER\Software\Hibara\AttacheCase
Warning
When manually operating registry,
sufficient knowledge and caution are necessary.
Please go only if you are confident.
Even if some kind of failure occurs in the system due to incorrect registry operation,
I can not assume the responsibility.
Even if the registry remains, there will be no problem with future operation.
Let's stop those who do not have confidence.
Limitation
If your operating system (OS) is 32 bit version,
the self-executable output will be limited to 4 GB or less.
This is due to the limitation that 32 bit OS will only recognize memory up to 4 GB.
In the AttachéCase, you can output an executable file of 4 GB or more,
but you can not run it on the 32 bit OS.
However, if you drag and drop the executable file directly to the AttachéCase,
you can decrypt it without problems.
If you forget your password
It will not do anything. Please give up. :)
I often get an e-mail about it, but even the author can not decrypt it.
The password character string is not included as it is in the encrypted file as a key,
but it is used as a shuffling "source" when encrypting it.
As the image is the same as "seasoning" put in cooking,
it is in a state of being completely melted and mixed with the soup.
Therefore, once you forget your password,
it will be impossible to extract passwords or restore from mixed files.
The high cryptographic strength has been proved,
and it is impossible for the author to decrypt it.
If it is encryption software that someone can decrypt it,
does not it make sense??
However, there may still be some people who want to decrypt it somehow.
Below are a few ways, but I will give you some examples.
Brute force script from the command line
In the AttachéCase, you can use command line options,
so you would solve it by a brute force attack by programing scripts and batch files.
If you have some knowledge of the program, you will be able to program it immediately.
Password brute force script
For scripts, there are VBA macros provided with Word and Excel,
Windows Scripting Host, and so on.
For details on how to make scripts and batch files,
please check with the internet etc ..
It is not in the range of "AttachéCase", so it is not supported.
I do not respond to inquiries about it.
"AttachéCase" is now
open source,
so there is also a last resort to develop brute force crack tool by yourself.
Is it faster to recall your password?
After all, these have limitations as well.
If the number of entered password characters is large,
the number of combinations will increase.
It will be awfully long to decrypt.
It might be that it is much more efficient to recall the password you forgot,
and the probability of decryption is high.
Conversely, on the premise that password management is done properly,
in order to create an encrypted file hard to be broken by an attacker,
it is necessary to input the password in consideration so that it can endure the
"Brute force script" attack.
You should devise various ways, such as entering long strings,
using the "
Password file
" function.
 NET Framework 4.5 later
NET Framework 4.5 later
 macOS 10.14 (macOS Mojave) later
macOS 10.14 (macOS Mojave) later